How confident are you that your software is truly secure against cyberattacks? Even a single vulnerability in your code can expose sensitive data, compromise user trust, and lead to financial losses. In today’s environment, where cyber threats evolve constantly, relying solely on traditional testing methods is no longer enough.
This is why penetration testing software has become an essential part of the software development process. Unlike standard testing, it proactively simulates real-world attacks to uncover hidden weaknesses in applications, networks, or systems. By identifying vulnerabilities before they are exploited, penetration testing helps developers deliver secure, resilient software that safeguards both users and business assets.
Overview of Penetration Testing Software
Penetration testing software is a specialized tool designed to evaluate the security of your applications, networks, and systems by simulating real-world cyberattacks. Unlike traditional testing methods, it goes beyond identifying functional bugs and focuses on uncovering hidden vulnerabilities that hackers could exploit. This proactive approach ensures that security weaknesses are detected early, helping developers fix them before they become critical threats.
Modern automated penetration testing software takes this process a step further by streamlining tests, reducing manual effort, and generating detailed reports with prioritized vulnerabilities. Whether it’s for internal systems, web applications, or mobile platforms, these tools provide actionable insights that strengthen security, maintain compliance, and reduce the risk of costly breaches.
5 Reasons Why Penetration Testing Software is Essential for Software Development
Ensuring the security of your software isn’t optional, it’s a critical part of delivering a reliable product that users can trust.
- Detect Vulnerabilities Early and Reduce Costs
Studies show that fixing a vulnerability during development costs up to30 times less than patching it after deployment. Penetration testing software helps developers identify and fix security gaps early in the software development lifecycle (SDLC).
By proactively testing applications, businesses avoid expensive post-release patches and potential financial losses from breaches.
- Protect Sensitive Data and Maintain Compliance
With43% of cyberattacks targeting small businesses and regulations like GDPR, HIPAA, and PCI DSS becoming stricter, securing sensitive data is critical.
Automated penetration testing software scans systems continuously, ensuring that vulnerabilities in personal, financial, or health-related data are detected and mitigated before attackers exploit them.
- Minimize Financial and Reputational Risks
A single breach can cost an average of$4.45 million, according to IBM’s Cost of a Data Breach Report 2023.
Implementing penetration testing software ensures your applications are resilient against attacks, reducing the likelihood of costly downtime, data theft, and damage to brand reputation.
- Improve Software Quality and Reliability
Vulnerabilities don’t just risk security – they can also affect functionality. Studies indicate that over 70% of applications have at least one critical security flaw at launch.
By using internal penetration testing software and other specialized tools, development teams can ensure that applications run smoothly while remaining secure, improving overall product quality and user trust.
- Stay Ahead of Evolving Cyber Threats
Cyber threats are constantlyincreasing, with over 2,200 attacks occurring every day on average. Web penetration testing software helps organizations simulate real-world attack scenarios and adapt to new vulnerabilities, ensuring that software remains secure even as hackers develop new attack techniques.
Investing in penetration testing software isn’t just about security, it’s about building trustworthy, high-quality software that protects both your business and your users.
What are the Process Involved in Penetration Testing
Penetration testing follows a structured process to identify and fix security weaknesses. Here are the six key steps:
- Planning and Scope Definition
The first step is to define what will be tested, such as networks, web applications, or internal systems. Goals, timelines, and rules of engagement are set to ensure the testing is safe and effective. - Reconnaissance (Information Gathering)
Testers collect information about the target system, like domain details, IP addresses, and system architecture. This step helpsidentify potential entry points that attackers could exploit. - Vulnerability Scanning
Using tools and software, includingautomated penetration testing software, testers scan the system for known vulnerabilities, weak configurations, and outdated software that may pose security risks. - Exploitation
This step involves safely exploiting the discovered vulnerabilities to see how far an attacker could penetrate the system. It helps understand the real-world impact of security flaws. - Post-Exploitation and Analysis
After exploiting vulnerabilities, testers analyze the results to understand the potential damage and risk level. This helps prioritize which vulnerabilities should be fixed first. - Reporting and Recommendations
A detailed report is created showing all vulnerabilities, their severity, and actionable recommendations. This report guides developers and IT teams on how to strengthen security effectively.
Common Challenges in Penetration Testing and How to Overcome Them
Even the most robust penetration testing processes can face obstacles, but understanding common challenges helps teams tackle them effectively.
1. Time-Consuming and Resource-Intensive Testing
Challenge: Traditional penetration testing can take weeks or even months, consuming significant time and IT resources. This can delay software releases and strain teams.
How to Overcome: Using automated penetration testing software can speed up the testing process, reduce manual effort, and allow continuous monitoring without affecting development timelines. Automation ensures faster identification of vulnerabilities while freeing up valuable team resources.
2. High Rate of False Positives
Challenge: Penetration tests often flag issues that aren’t actual threats, causing teams to spend time investigating non-critical problems. False positives can reduce the efficiency of security efforts.
How to Overcome: Choose best penetration testing software with high accuracy and reliable reporting. Combine automated tools with expert human analysis to validate vulnerabilities, ensuring focus on real risks and effective remediation.
3. Limited Coverage of Complex Systems
Challenge: Modern applications often include web, mobile, and internal systems. Testing all these layers thoroughly can be challenging, leaving some areas exposed.
How to Overcome: Leverage a combination of internal penetration testing software and web penetration testing software to cover all environments. Structured testing plans and regular reviews ensure comprehensive security coverage across the entire infrastructure.
By anticipating these challenges and using the right tools and strategies, organizations can ensure penetration testing is effective, efficient, and delivers real security improvements.
How Often Do You Need to Run Penetration Testing?
Penetration testing is not a one-time activity, software and cyber threats are constantly growing. Ideally, testing should be conducted after every major update, feature release, or system upgrade to ensure new vulnerabilities are not introduced. Regular testing also helps maintain compliance with industry standards like GDPR, HIPAA, and PCI DSS.
For dynamic applications or web platforms, organizations can leverage automated penetration testing software for continuous monitoring. Many security experts recommend running comprehensive penetration tests at least quarterly or bi-annually, while high-risk systems may require monthly or even ongoing assessments. Consistent testing ensures your software remains secure, resilient, and trusted by users.
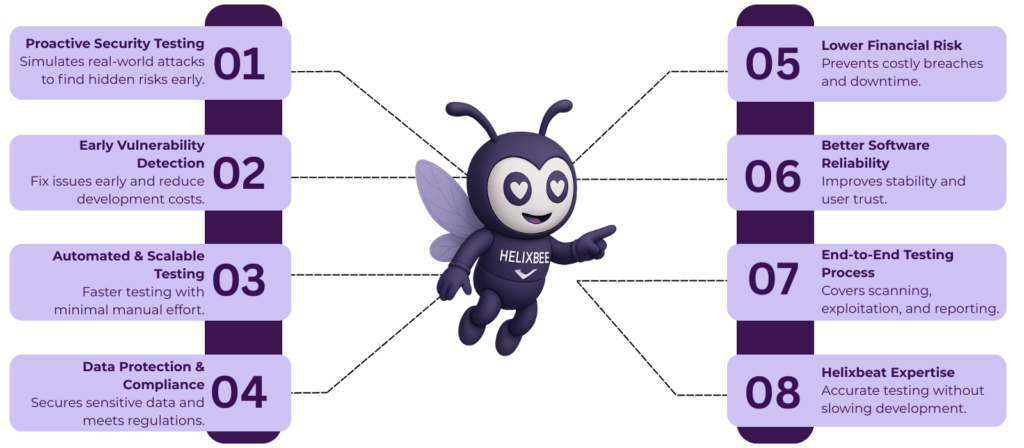
Why Choose Helixbeat for Penetration Testing Services?
Choosing the right partner for penetration testing is important to keep your software safe and reliable. At Helixbeat, we use advanced penetration testing software and expert knowledge to find vulnerabilities in web, mobile, and internal systems. Our goal is to help you fix security gaps before they become a problem.
Here’s why Helixbeat is different:
- We use automated penetration testing software for faster and more accurate checks.
- Our team works with internal penetration testing software and web penetration testing software to cover all parts of your system.
- We provide clear reports that show which issues need fixing first.
- Our experts perform testing without slowing down your development.
With Helixbeat, you get reliable and thorough penetration testing that keeps your software and users safe. Secure your software today
What Users Say About AERIS
Dr. Sarah L.
Hospital Administrator
John T.
Telemedicine Provider
Emily P.
Healthcare Executive
Frequently Asked Questions
- What is penetration testing software and why is it important?
Penetration testing software simulates cyberattacks on your systems to find vulnerabilities before hackers do. It helps protect sensitive data,maintain compliance, and reduce the risk of costly breaches. - What is the difference between automated and manual penetration testing?
Automated penetration testing software speeds up the process, scans continuously, and reduces human effort, while manual testing relies on experts to find complex vulnerabilities that automation might miss.Both together give the best results. - How often should I run penetration tests on my software?
It depends on your software and updates, but most experts recommend running tests at least quarterly or after major releases. For high-risk systems, monthly or continuous automated testing is ideal. - Can penetration testing software protect both internal systems and web applications?
Yes.Internal penetration testing software focuses on your internal networks, while web penetration testing software secures your websites and web apps. Using both ensures complete coverage. - Why should I chooseHelixbeatfor penetration testing services?
Helixbeat combines advanced penetration testing software with expert analysis. We provide accurate, fast, and thorough testing for web, mobile, and internal systems, helping you fix vulnerabilities before they become threats.