Data compliance isn’t just a checkbox—it’s a big deal, especially in visitor management.
With regulations like GDPR and CCPA now firmly in place, businesses can’t afford to take data privacy lightly. It’s not just about avoiding fines; it’s about earning trust. People care about their personal information—92% of consumers expect companies to be proactive about protecting it. That means businesses need to step up and ensure their systems handle visitor data responsibly.
But here’s the challenge: Where is all that sensitive visitor data stored? Who can access it? How long is it kept before it’s deleted? These are the questions every organization should be asking before adopting an electronic visitor management systems. Because at the end of the day, compliance isn’t just a legal requirement—it’s about respecting people’s privacy and building lasting relationships based on trust.
In this blog, we’ll enlighten you about data privacy and compliance with visitor management systems.
Table of Contents
Importance of Global Regulations in Visitor Management Systems
A Visitor Management Systems (VMS) collects sensitive information such as names, contact details, identification documents, and visit logs. If mishandled, this data can be vulnerable to breaches, leading to legal and reputational risks. Global regulations exist to protect personal data, ensuring businesses adopt strict data protection measures. A compliant VMS like VISTA helps organizations:
- Enhance Data Security: Prevent unauthorized access and misuse of visitor data.
- Build Trust: Establish transparency with visitors regarding data collection and usage.
- Avoid Legal Penalties: Stay compliant to prevent hefty fines and legal actions.
- Ensure Operational Efficiency: Streamline data processing while adhering to legal norms.
- Support Ethical Business Practices: Align with global data privacy standards to maintain corporate integrity
In 2019, a leading European tech company faced a €10 million GDPR fine due to a electronic visitor management systems (VMS) data breach that exposed thousands of visitor records. The breach occurred because visitor data was stored in an unencrypted cloud database, making it vulnerable to unauthorized access. Additionally, the company collected excessive visitor information, violating GDPR’s data minimization rule, and failed to implement proper access restrictions, allowing employees without security clearance to view and export sensitive records. Another major issue was the lack of an automated data deletion policy, resulting in visitor records being stored indefinitely. As a result, the company suffered severe reputational damage, losing customer trust and facing operational disruptions.
To rectify the situation, they had to completely overhaul their VMS, implementing secure data storage, role-based access control, and automated deletion policies. This case highlights the critical importance of data privacy in visitor management. A privacy-first VMS like VISTA by Helixbeat ensures compliance with global regulations, enhances security, and protects visitor information through encrypted storage, strict access controls, and automated data retention policies, preventing legal consequences and safeguarding business reputation.
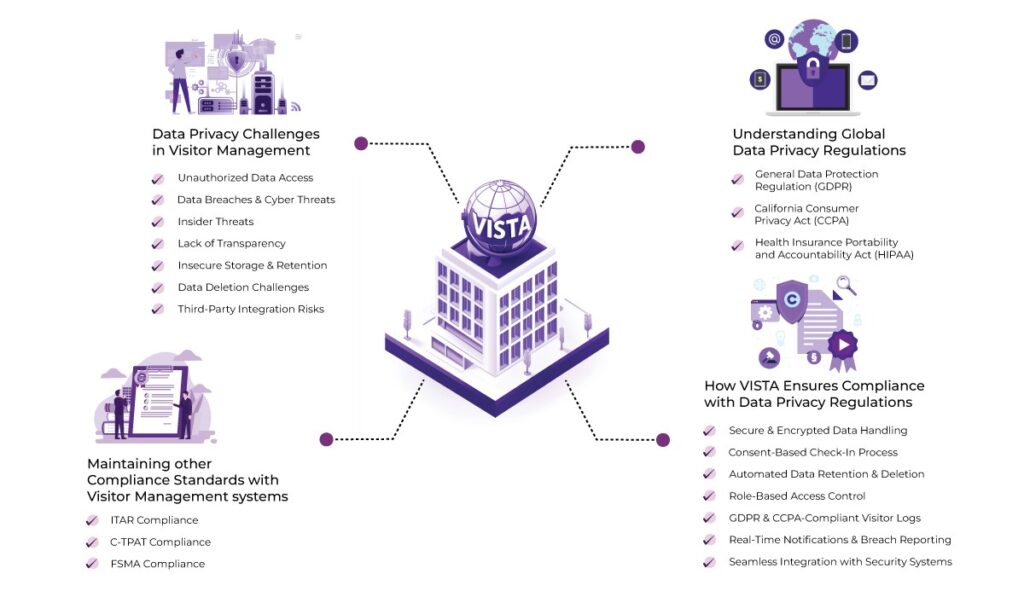
Data Privacy Challenges in Visitor Management
- Unauthorized Data Access – Weak authentication and lack of role-based permissions can expose sensitive visitor data, increasing the risk of breaches.
- Data Breaches & Cyber Threats – Hackers use phishing, SQL injection, and malware to steal visitor data. Without strong cybersecurity, organizations risk privacy violations.
- Insider Threats – Employees with unrestricted access may misuse or leak visitor data. Role-based controls and monitoring help prevent internal threats.
- Lack of Transparency – Visitors often remain unaware of how their data is collected or used. Clear privacy policies and consent forms build trust and compliance.
- Insecure Storage & Retention – Poor encryption and indefinite data storage increase security risks. Strict retention policies and encryption are essential.
- Data Deletion Challenges – Inefficient handling of deletion requests can lead to non-compliance. Automated processes ensure proper data erasure under GDPR/CCPA.
- Third-Party Integration Risks – Weak integrations can expose data. Vetting third-party vendors ensures compliance with security standards.
Understanding Global Data Privacy Regulations
1. General Data Protection Regulation (GDPR)
The European Union’s GDPR is one of the most comprehensive data protection laws, focusing on transparency, consent, and user control. It mandates organizations to:
- Obtain explicit consent before collecting personal data.
- Securely store and process data with encryption.
- Allow visitors to request data access, correction, or deletion.
- Report data breaches within 72 hours.
2. California Consumer Privacy Act (CCPA)
CCPA grants California residents greater control over their personal data, requiring businesses to:
- Disclose data collection and usage practices.
- Offer an opt-out option for data selling.
- Provide access to collected data upon request.
- Maintain high data security standards to prevent breaches.
3. Health Insurance Portability and Accountability Act (HIPAA)
For healthcare facilities, HIPAA compliance is essential. It mandates:
- Strict access control to patient and visitor data.
- Data encryption to prevent unauthorized access.
- Clear policies on data retention and deletion.
Maintaining other Compliance Standards (C-TPAT, ITAR, FSMA) with Visitor Management systems
Below are other three types of compliance an electronic visitor management systems can help your organization to comply with–
ITAR Compliance: The International Traffic in Arms Regulations (ITAR) is a set of laws designed to prevent sensitive and classified data from being accessed by foreign entities. It mandates strict monitoring of individuals entering a facility and the secure management of confidential organizational data. Implementing an electronic visitor management systems can help organizations adhere to ITAR compliance by ensuring proper tracking and security measures.
C-TPAT Compliance: The Customs-Trade Partnership Against Terrorism (C-TPAT) sets security standards for supply chains to prevent disruptions when goods reach the border. To comply with these regulations, visitor management systems must incorporate practices such as capturing visitor photos upon arrival, issuing automated badges, and maintaining digital visitor logs. These measures help uphold data privacy and security standards.
FSMA Compliance: The Food Safety Modernization Act (FSMA) is a regulatory framework established by the FDA to enforce food safety practices and procedures. Food companies must monitor visitors to ensure compliance with FDA safety standards while also maintaining a secure and welcoming environment. An electronic visitor management systems can support FSMA compliance by implementing strategies such as touchless check-in and check-out processes, verifying identification, conducting visitor and thermal screenings, and alerting hosts in case of unauthorized access.
How VISTA Ensures Compliance with Data Privacy Regulations
VISTA by Helixbeat is designed to address compliance challenges and offer businesses a seamless, secure, and privacy-focused visitor management systems. Here’s how VISTA helps organizations meet global data privacy regulations while ensuring a smooth visitor experience.
1. Secure & Encrypted Data Handling
VISTA prioritizes data security by using advanced encryption techniques to protect all visitor information. This means that even if data is intercepted, it remains unreadable to unauthorized users. By following industry-standard security protocols, VISTA minimizes the risk of data breaches and cyber threats. Businesses using VISTA can be confident that visitor records are stored safely and are accessible only to authorized personnel.
2. Consent-Based Check-In Process
Before collecting any visitor information, VISTA ensures that explicit consent is obtained. This means that visitors are fully informed about how their data will be used and stored. Businesses can customize consent forms to align with specific regulations such as GDPR (General Data Protection Regulation) or CCPA (California Consumer Privacy Act). This feature ensures that organizations remain compliant while giving visitors control over their personal data.
3. Automated Data Retention & Deletion
One of the key compliance requirements in data privacy laws is that personal data should not be stored indefinitely. VISTA allows businesses to set automatic data retention and deletion policies. This means visitor data is only stored for as long as necessary and is automatically deleted once it is no longer needed. By following regulations such as GDPR and CCPA, VISTA helps organizations minimize compliance risks and avoid penalties for improper data handling.
4. Role-Based Access Control
Not everyone in an organization needs access to visitor data. VISTA implements role-based access control (RBAC), ensuring that only authorized personnel can view or manage visitor records. This feature prevents unauthorized access and helps businesses maintain strict data security. Additionally, multi-layer authentication adds an extra level of protection, reducing the chances of internal data misuse.
5. GDPR & CCPA-Compliant Visitor Logs
VISTA provides visitors with full control over their data, in line with GDPR and CCPA requirements. Visitors can request access to their information, modify it, or ask for its deletion at any time. This ensures transparency and gives individuals greater control over their personal information. Additionally, VISTA maintains detailed audit trails, so businesses can track data access and modifications, providing proof of compliance when required.
6. Real-Time Notifications & Breach Reporting
In case of any suspicious activity or potential data breach, VISTA sends instant alerts to administrators. This allows businesses to respond quickly and take necessary action to prevent unauthorized access or data leaks. Many data privacy laws require companies to report breaches within a specific timeframe, and VISTA helps organizations comply by enabling fast and efficient breach reporting.
7. Seamless Integration with Security Systems
VISTA is designed to work alongside existing security infrastructure, such as access control and surveillance systems. By integrating with these systems, VISTA provides a holistic security approach that reduces compliance gaps. Businesses can ensure that their visitor management system functions as part of a broader security strategy, helping them stay compliant while improving overall workplace safety.
Final words
It is clear that companies should employ optimal electronic visitor management systems to comply with data regulations and standards. Visitor Management systems can help companies manage different visitor types, provide pre-registration and identification control, limit visitor access to approved areas,and deliver compliance and data security.
So,go for a secure and best Visitor Management system like VISTA to make your facility compliant and efficient. VISTA enhances workplace security, ensures legal compliance, makes the management process seamless, and more.
Frequently asked question
1. What are the key data privacy regulations affecting visitor management systems?
GDPR (EU), CCPA (US), HIPAA (US), and PDPA (various countries) regulate how visitor data is collected, stored, and used. Non-compliance can lead to hefty fines and legal issues.
2. How can visitor management systems ensure compliance with GDPR and CCPA?
By collecting only necessary data, obtaining explicit consent, allowing data access/deletion requests, encrypting data, and regularly auditing compliance.
3. What are the risks of not complying with data privacy laws?
Fines, legal action, data breaches, identity theft, and loss of customer trust.
4. How do visitor management systems handle data retention and deletion?
They automatically delete data after a set period, allow visitor-requested deletions, maintain audit logs, and enforce role-based access controls.
5. What security measures protect visitor data?
Encryption, multi-factor authentication, role-based access control, real-time monitoring, and regular security audits.
6. How do visitor management systems obtain and manage visitor consent?
Through clear privacy policies, digital consent forms, opt-in/opt-out options, and timestamped records of consent.
7. Why is encryption important in visitor management systems?
Encryption secures stored and transmitted data, preventing unauthorized access and data breaches.
8. How can businesses ensure third-party integrations comply with data privacy laws?
By vetting providers for compliance, using Data Processing Agreements (DPA), auditing integrations, and restricting unnecessary data sharing.