Outsourcing custom software development is a powerful strategy for U.S. businesses seeking efficiency, scalability, and innovation. However, security risks remain a top concern, with nearly 60% of outsourced projects reporting potential breaches or vulnerabilities.
Helixbeat is a trusted partner where U.S. organizations can confidently outsource software development, including web application development outsourcing, while adhering to strict security standards. From protecting sensitive data to ensuring regulatory compliance, businesses need robust practices to mitigate risks effectively.
This guide outlines seven essential security best practices that U.S. companies should implement when outsourcing custom software development to guarantee safe, efficient, and successful software delivery.
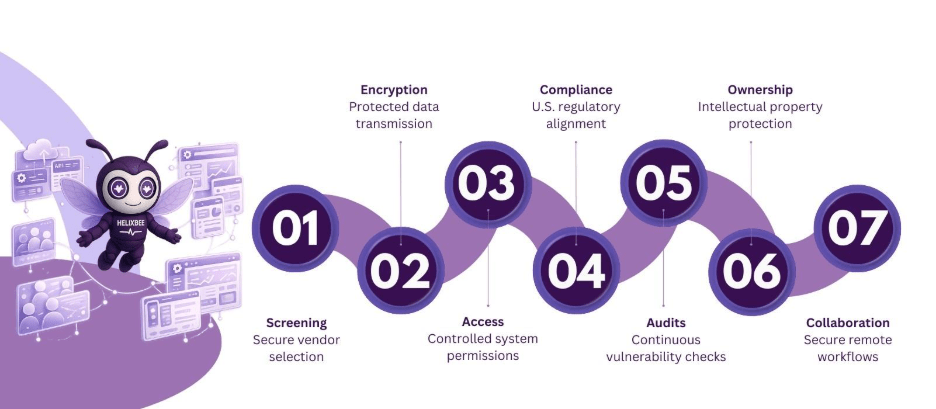
Table of Contents
1. Prioritize Vendor Security Screening Before Outsourcing
Choosing the right partner is the first step to secure custom software development outsourcing. Not all vendors maintain strong security protocols, and selecting the wrong one can expose your business to unnecessary risks.
Key Screening Practices
Before you outsource custom software development services, verify vendor certifications, check prior project security performance, and review how they handle, store, and control access to sensitive data. These steps ensure that your data and intellectual property remain protected.
Impact on U.S. Businesses
Companies that perform thorough vendor screening reduce the risk of data breaches by up to 50%, safeguarding business information and protecting long-term operations.
2: Implement Strong Data Encryption and Secure Communication
Sensitive information must remain secure during web application development outsourcing, whether in transit or storage. Strong encryption and secure communication prevent unauthorized access.
Recommended Encryption Practices
Use AES-256 encryption for stored data, HTTPS/TLS 1.3 for apps, and encrypt sensitive database and API information. These measures protect critical business and customer data from cyber threats.
Benefits of Encryption
Proper encryption ensures intercepted data cannot be read, giving U.S. businesses confidence when they outsource custom software development.
3: Enforce Access Control and Role-Based Permissions
Limiting system access reduces insider threats and prevents unauthorized activities.
Best Practices for Access Management
Assign roles based on job responsibilities, implement multi-factor authentication, and review access privileges regularly to maintain tight security when you outsource custom software development services.
Real-World Advantage
U.S. companies enforcing strict access controls report 40% fewer unauthorized access incidents, ensuring business continuity and safety.
4: Ensure Regulatory Compliance in Outsourced Development
Compliance with U.S. laws protects businesses from penalties and builds client trust.
Key Compliance Standards
Adhere to HIPAA, PCI DSS, or CCPA requirements as needed. A custom software development outsourcing partner should integrate these standards from the start.
Benefits of Compliance
Maintaining compliance strengthens credibility, reduces legal risk, and enhances long-term reputation while outsourcing custom software development.
5: Conduct Regular Security Audits and Penetration Testing
Continuous monitoring ensures vulnerabilities are caught before attackers exploit them.
Recommended Audit Practices
Schedule quarterly security audits, perform penetration testing after major updates, and review code repositories for potential risks when you outsource custom software development services.
Business Impact
Proactive audits can reduce security incidents by nearly 50%, protecting both project timelines and critical business data.
6: Protect Intellectual Property in Outsourced Projects
IP is often the most valuable asset when you outsource custom software development.
IP Protection Measures
Use strong NDAs, monitor repository access, and include code ownership clauses in contracts. These measures secure your competitive advantage and prevent disputes.
Advantages of IP Security
Protecting intellectual property ensures businesses retain control over their innovations and avoid costly legal issues.
7: Secure Remote Collaboration for Web Application Development Outsourcing
Remote teams are common, but unsecured workflows increase risk.
Best Practices for Remote Security
Use end-to-end encrypted communication tools, enable MFA on all platforms, and train teams in cybersecurity awareness and phishing prevention.
Proven Results
Organizations that implement secure remote collaboration report 35% fewer security incidents during outsourced projects, keeping software delivery safe and reliable.
Helixbeat Development Services – A Trusted Partner for U.S. Businesses
Helixbeat is a trusted development services company where U.S. organizations can confidently outsource custom software development services while maintaining high security and operational standards. Partnering with a reliable provider ensures that projects stay on schedule, scalable, and fully compliant.
What Helixbeat Offers
- Expertise in secure web application development outsourcing for U.S. businesses
- Encrypted data storage, secure APIs, and robust authentication protocols
- Regular security audits and vulnerability assessments to prevent breaches
- Compliance support for HIPAA, PCI DSS, and CCPA standards
- Dedicated account managers providing transparency, timely updates, and accountability
Why Helixbeat Stands Out
With a proven track record and 99% client retention, Helixbeat delivers high-quality custom software development outsourcing solutions that are secure, efficient, and aligned with U.S. business goals.
Wrapping Up
Outsourcing custom software development services can accelerate growth, but security and compliance must remain priorities. By following these seven best practices and partnering with Helixbeat, U.S. businesses can confidently protect sensitive data, achieve reliable project outcomes, and scale operations efficiently.
Contact Helixbeat today to outsource safely and securely.
FAQs
1. How can U.S. companies’ vet offshore vendors for security compliance?
Look for ISO 27001/SOC 2 certifications, review past security audits, and request detailed documentation of security protocols.
2. Are cloud-based outsourced projects safe for sensitive data?
Yes, if strong encryption, MFA, and secure APIs are implemented.
3. How often should outsourced software be tested for vulnerabilities?
Conduct quarterly security audits and penetration testing after major updates.
4. What legal protections safeguard IP in outsourced development?
NDAs, IP ownership clauses, and strict repository access logs protect intellectual property.
5. How does Helixbeat ensure secure outsourcing for U.S. clients?
Through encryption, compliance adherence, continuous monitoring, and dedicated account management.
6. What is the biggest hidden risk in web application development outsourcing?
Weak coding practices and unmonitored repository access can expose sensitive data and IP.
7. Can small businesses outsource securely without high costs?
Yes, by choosing certified vendors, enforcing access control, and following best security practices.