Table of Contents
Introduction
Security today isn’t just about locking doors—it’s about knowing exactly who is entering your premises, why they are there, and how long they stay. Yet, many organizations still rely on outdated paper logs or basic check-in processes that leave gaps in security and accountability.
In a world where data breaches, workplace safety, and compliance requirements are rising, businesses need a smarter approach. This is where a visitor authentication and management system becomes essential.
Whether you’re managing a corporate office, hospital, or multi-location enterprise in the USA, implementing a visitor authentication and management system is no longer optional—it’s a necessity. It not only strengthens security but also enhances the visitor experience and streamlines operations.
In this blog, we’ll walk you through how a visitor authentication and management system works—from check-in to exit—so you can understand how it transforms your front desk into a secure, efficient, and intelligent control point.
What is a Visitor Authentication and Management System?
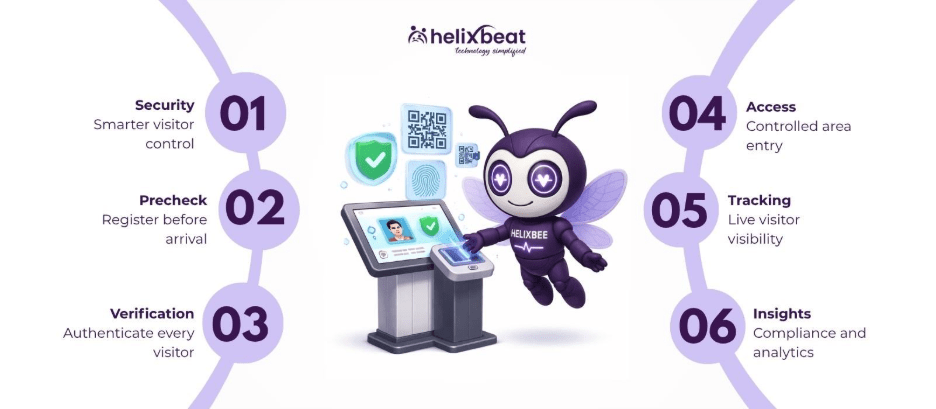
A visitor authentication and management system is a digital solution that verifies, tracks, and manages visitors entering a facility.
Unlike manual registers, a digital visitor management system automates the entire process—from identity verification to real-time tracking—ensuring that only authorized individuals gain access.
For organizations looking for the best visitor management system, the focus is not just on recording entries but on controlling access, ensuring compliance, and improving efficiency.
Why Businesses in the USA Are Adopting Visitor Authentication Systems
Organizations across the United States are rapidly shifting toward advanced systems due to:
- Increasing workplace security concerns
- Compliance requirements (HIPAA, OSHA, etc.)
- Hybrid work environments
- High visitor volumes in offices and healthcare facilities
A visitor access management system helps organizations handle these challenges while maintaining a seamless experience for guests.
Step-by-Step: How a Visitor Authentication and Management System Works
Let’s break down the entire journey—from the moment a visitor plans their visit to when they exit the facility.
Step 1: Pre-Registration (Before Arrival)
Modern systems allow visitors to pre-register before they even arrive.
- Visitors receive an invite via email or SMS
- They enter their details and upload ID proof
- A QR code is generated for quick entry
This is where a visitor authentication and management system begins its work—by collecting and validating data early.
For organizations using a visitor management system for office, this step reduces congestion at reception and improves planning.
Step 2: Arrival and Check-In
When the visitor arrives:
- They scan their QR code or enter details at a kiosk
- The system retrieves pre-filled information
- Walk-in visitors can register on the spot
A digital visitor management system ensures that check-in is fast, contactless, and accurate.
Compared to manual logs, a visitor authentication and management system reduces wait times significantly while maintaining a professional first impression.
Step 3: Identity Verification
This is the most critical stage.
A visitor authentication and management system verifies the visitor’s identity using:
- OTP verification
- ID scanning
- Photo capture
- Facial recognition (optional)
This ensures that only genuine visitors are allowed entry.
For businesses seeking the best visitor management system, strong authentication capabilities are non-negotiable.
A visitor access management system also checks if the visitor is pre-approved or flagged, adding an extra layer of security.
Step 4: Host Notification
Once the visitor is verified:
- The host receives an instant notification via email, SMS, or app
- The host can approve or deny access
A visitor authentication and management system eliminates the need for receptionists to manually call employees.
This feature is especially useful in a visitor management system for office, where employees may be in meetings or working remotely.
Step 5: Badge Printing and Access Control
After approval:
- A visitor badge is printed automatically
- Access permissions are assigned based on the visit purpose
A visitor access management system ensures that visitors can only enter authorized areas.
For example:
- A vendor may access only service zones
- A client may access meeting rooms
- A candidate may be restricted to HR areas
This level of control is what makes a visitor authentication and management system essential for modern workplaces.
Step 6: Real-Time Visitor Tracking
Once inside, the system continues to monitor the visitor.
- Tracks entry and exit times
- Maintains live visitor logs
- Provides visibility into who is on-site
A digital visitor management system enables security teams to respond quickly in case of emergencies.
Organizations using the best visitor management system benefit from real-time insights that improve operational awareness.
Step 7: Compliance and Data Storage
Every interaction is recorded and stored securely.
A visitor authentication and management system helps organizations:
- Maintain audit trails
- Meet regulatory requirements
- Ensure data privacy
In industries like healthcare, compliance is critical. A visitor access management system ensures that all visitor data is handled securely and responsibly.
Step 8: Check-Out and Exit Management
When the visit ends:
- Visitors check out via kiosk or mobile
- The system records exit time automatically
- Hosts may receive a notification
A visitor authentication and management system ensures no visitor remains untracked inside the premises.
This is a major improvement over manual systems, where exits are often not recorded properly.
Step 9: Analytics and Reporting
After the visit, the system generates insights such as:
- Visitor frequency
- Peak visiting hours
- Visitor categories
- Security incidents
A digital visitor management system turns raw data into actionable insights.
For businesses evaluating the best visitor management system, analytics play a crucial role in decision-making.
Benefits of a Visitor Authentication and Management System
Implementing a visitor authentication and management system offers multiple advantages:
1. Enhanced Security
Ensures only verified individuals gain access
2. Improved Efficiency
Automates repetitive tasks and reduces workload
3. Better Visitor Experience
Fast, contactless, and professional check-in
4. Compliance Readiness
Maintains secure and audit-ready records
5. Real-Time Visibility
Know exactly who is on-site at any moment
A visitor access management system brings together security, efficiency, and experience into one seamless solution.
Why VISTA is the Right Choice
For organizations in the USA looking for the best visitor management system, VISTA stands out as a powerful solution.
VISTA is a visitor authentication and management system designed to:
- Automate visitor workflows
- Strengthen security protocols
- Provide real-time visibility
- Ensure compliance with industry standards
As a digital visitor management system, VISTA offers:
- Contactless check-in
- Smart authentication
- Seamless integrations
- Multi-location management
Whether you need a visitor management system for office environments or complex enterprise setups, VISTA adapts to your needs.
Final Thoughts
The way organizations manage visitors has evolved significantly. Manual processes are no longer sufficient in a world that demands speed, security, and accountability.
A visitor authentication and management system transforms your front desk into a smart security hub—handling everything from identity verification to real-time tracking and compliance.
From check-in to exit, every step becomes seamless, secure, and efficient.
For businesses in the USA aiming to improve workplace safety, enhance visitor experience, and maintain compliance, adopting a visitor authentication and management system is a strategic move.
Solutions like VISTA don’t just manage visitors—they redefine how organizations approach security and operations in the modern era.
FAQs
1. What is a visitor authentication and management system?
A visitor authentication and management system is a digital solution that verifies, tracks, and manages visitor access to ensure security and efficiency.
2. How does a digital visitor management system improve security?
A digital visitor management system uses ID verification, real-time tracking, and access control to prevent unauthorized entry and enhance workplace safety.
3. What features should the best visitor management system have?
The best visitor management system should include pre-registration, identity verification, badge printing, real-time tracking, and analytics.
4. Is a visitor management system for office necessary in the USA?
Yes, a visitor management system for office environments helps meet compliance requirements, improve security, and streamline visitor handling.
5. How does a visitor access management system control entry?
A visitor access management system assigns role-based permissions, ensuring visitors can only access authorized areas within a facility.